

Strategic solutions in governance, risk, and compliance.
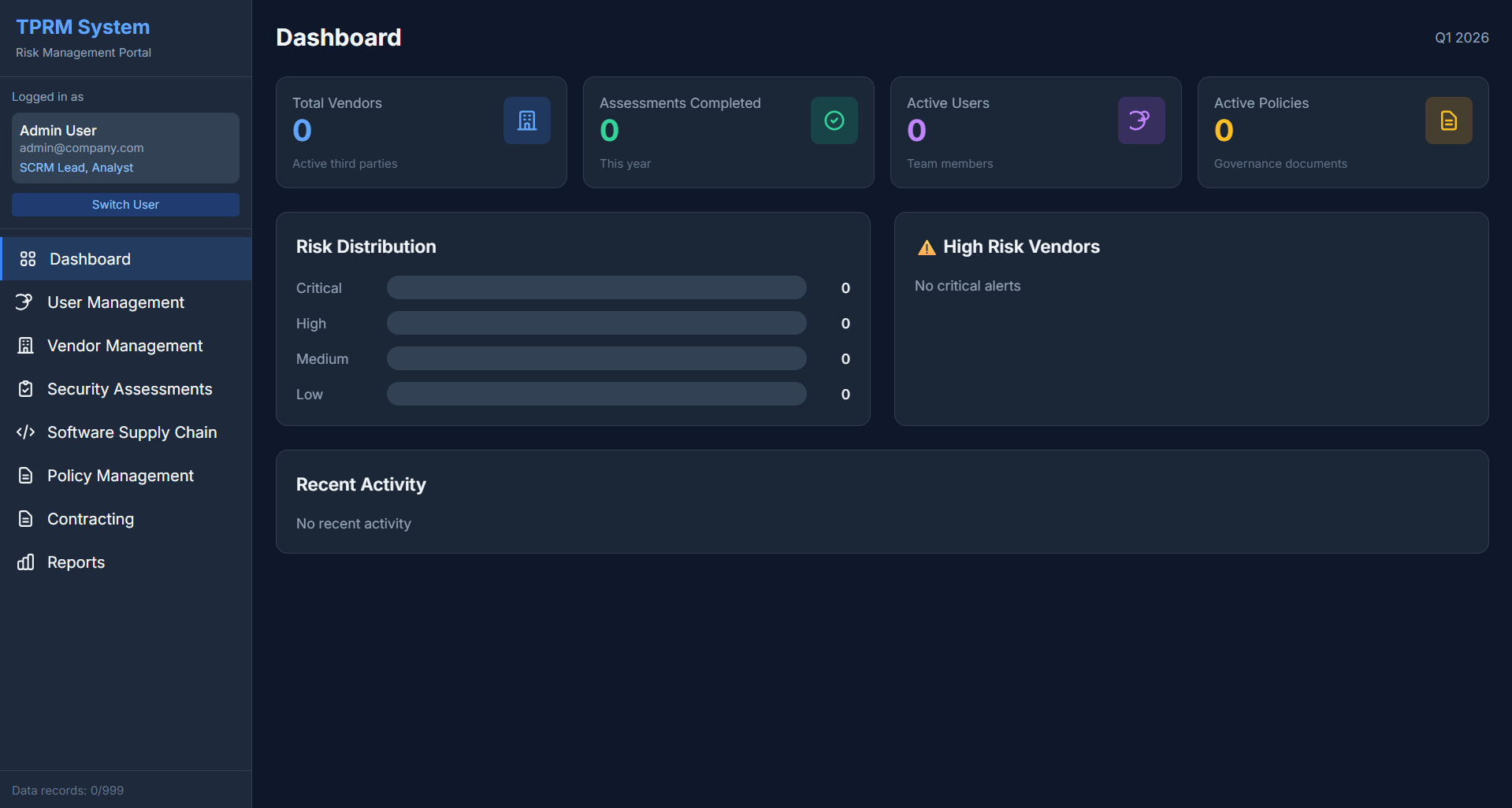
Architected and deployed an enterprise-wide risk management framework supporting ISO 27001, NIST CSF 2.0, and SOC 2 compliance across multiple business units.
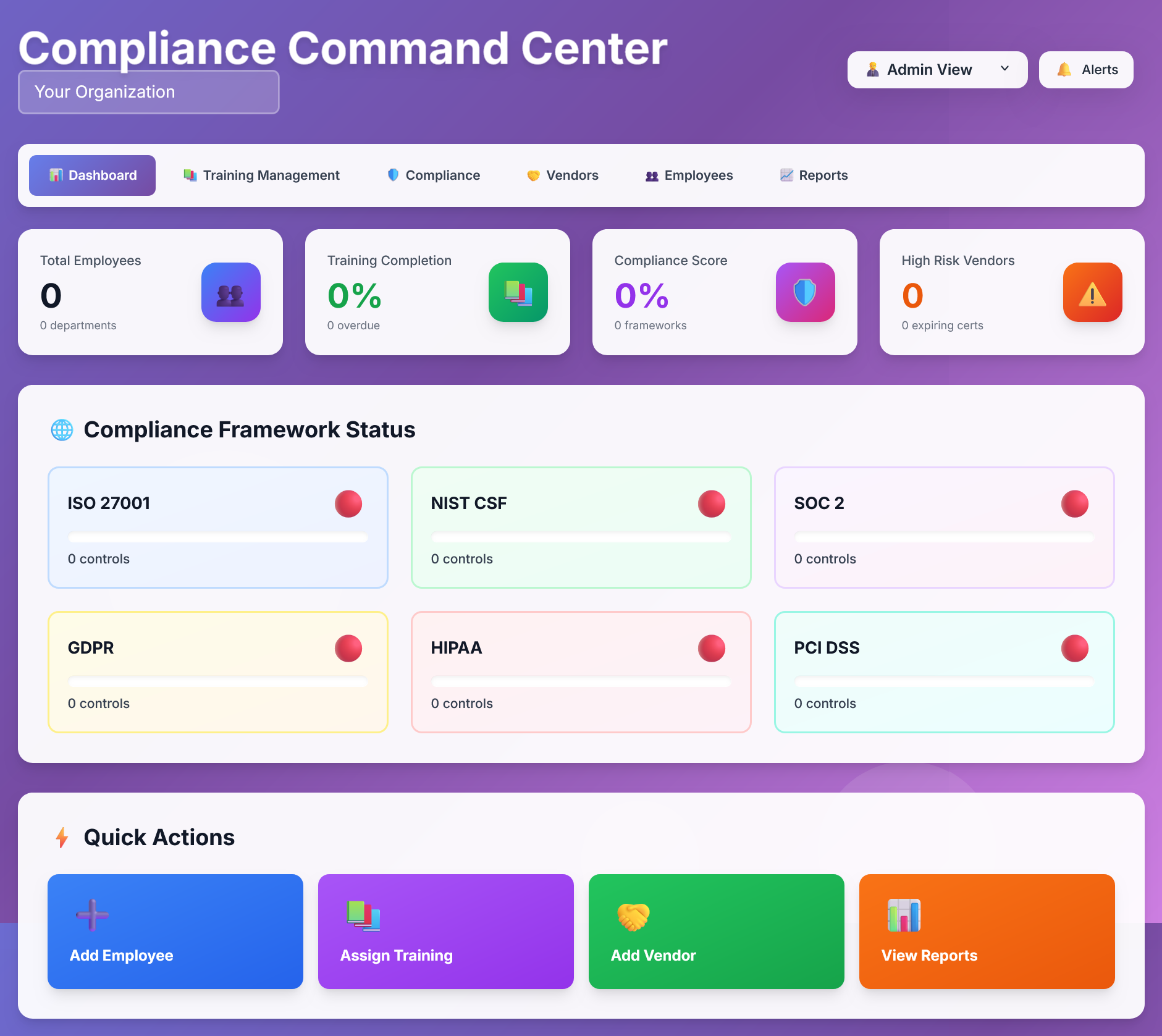
A comprehensive compliance management solution built in under 6 hours to prove that skills should make work easier, not harder.
🎯 Track Record
0 major audit findings | 40% risk reduction | 250+ locations secured
📊 Impact
Enterprise frameworks deployed | 20+ vendors managed | 35% security awareness improvement
✓ All credentials verified and current
Certifications actively maintained with regular professional development
Download my professional resume to learn more about my qualifications, experience, and achievements.
Comprehensive overview of my career, certifications, and expertise in GRC and cybersecurity
✓ Document Information
Format: PDF | Size: Professional & Concise
Strategic Solutions in Governance, Risk, and Compliance.
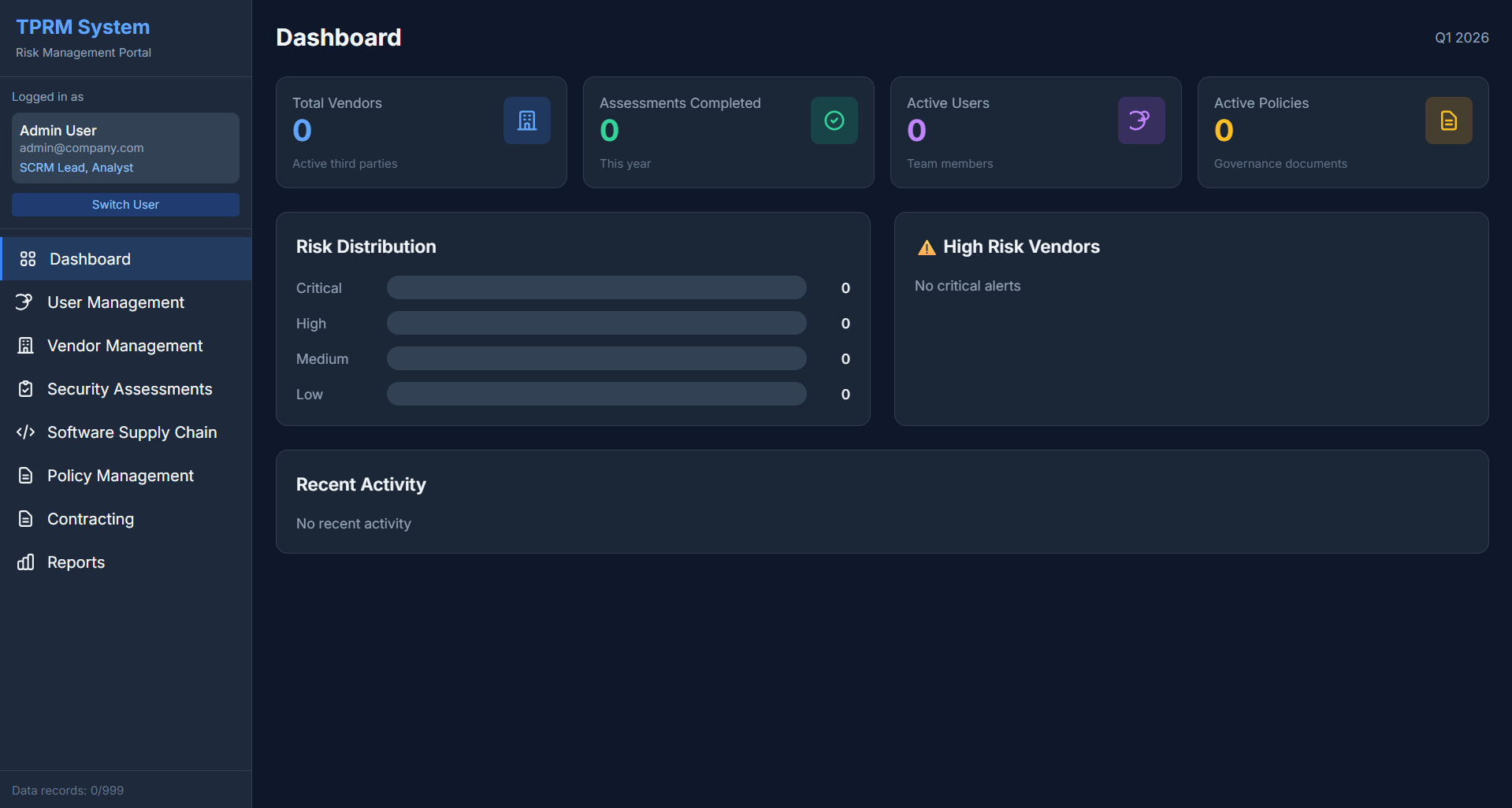
Architected and deployed an enterprise-wide risk management framework supporting ISO 27001, NIST CSF 2.0, and SOC 2 compliance across multiple business units.
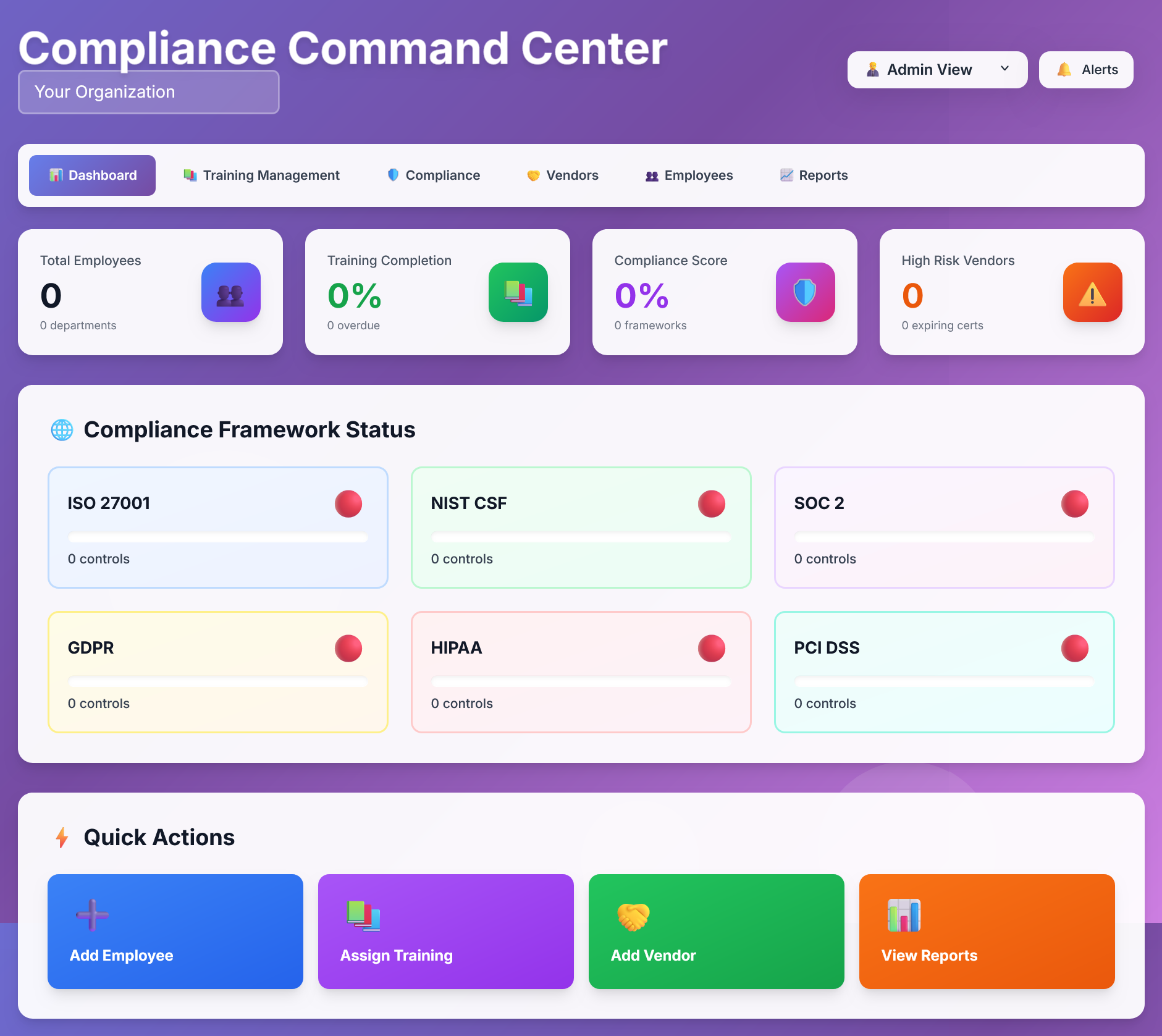
A comprehensive compliance management solution built in under 6 hours, demonstrating rapid deployment of enterprise-grade control systems.
Built a random number generator that shows outputs random amount from the population size.
View Details →Directed an accelerated NIST Cybersecurity Framework (CSF) implementation for a mid-sized healthcare organization facing urgent HIPAA compliance risks.
View Details →Leveraging technology to streamline GRC processes and enhance operational efficiency
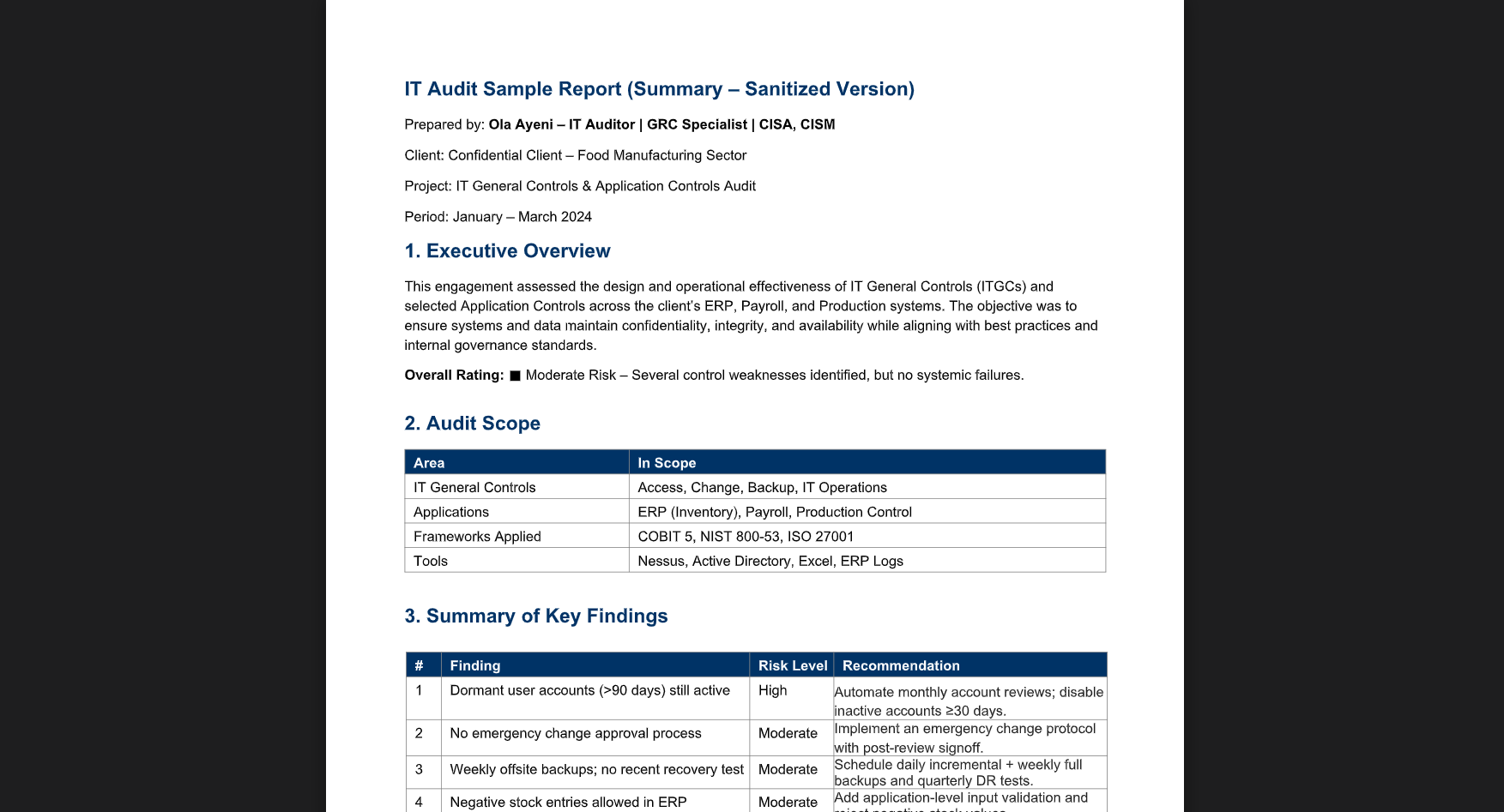
This engagement assessed the design and operational effectiveness of IT General Controls (ITGCs) and selected Application Controls across the client’s ERP, Payroll, and Production systems.
View File →Many organizations believe their Data Loss Prevention (DLP) strategy is airtight — firewalls, endpoint agents, encrypted data, access controls. But there’s a new insider threat quietly bypassing all of it: employees using artificial intelligence tools, often without approval, and unknowingly exfiltrating sensitive data.
View Details →